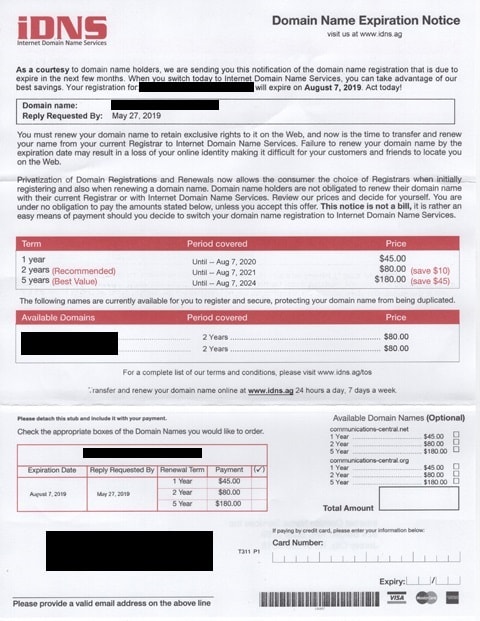
Scam PSA: "Domain Name Expiration/Renewal Notice"

This post is the third in our ongoing series about computer scams.
Ugh, scammers. They are a persistent problem with no real solution (permanently discourage one and hide the body, and you won’t even daunt the others). The best we can really do is make sure everyone can identify the scams when they come along.
For example, Ruth Thaler-Carter recently sent me a scam bill she got in the mail. This scammer preys on the unwary by looking up the contact details for a website, and then sending a bill to the mailing address listed in the fine print.
In today’s example, the scammer is trying to convince us to pay them to renew our domain registration. Obviously the domain is not expiring, and was not registered through the scammer in the first place, but the scammer knows that at least a few people will fall for the fake bill.
Why do they do this, you ask?
Because it works. While individuals don’t usually fall for this scam, send this kind of fake bill to a business and they will pay it almost without thinking. The mail room will forward it to accounts payable, where it will be added to the stack of bills and paid almost automatically.
This type of scam works so well in fact that one scammer bilked Facebook and Google out of $122 million over a three year period.
Rimasauskas’s grift was pretty bold. He merely sent Google and Facebook invoices for items they hadn’t purchased and that he hadn’t provided, which the companies paid anyway. The invoices were accompanied by "forged invoices, contracts, and letters that falsely appeared to have been executed and signed by executives and agents of the Victim Companies, and which bore false corporate stamps embossed with the Victim Companies’ names, to be submitted to banks in support of the large volume of funds that were fraudulently transmitted via wire transfer." He also spoofed emails that appeared to come from corporate execs.

Comments
Lynn April 2, 2019 um 10:05 pm
Just an FYI, but you missed the first mention of the domain name in question in the first paragraph of the notice. Thought I’d mention it since the rest are blacked out and I assume that means you don’t want it visible. 🙂
Nate Hoffelder April 3, 2019 um 8:19 am
It’s not that important. I just wanted to block out the mailing address, and took it a step further. Thanks for pointing it out; I went back and covered all 3 of the details I missed before.
Jeffrey April 27, 2019 um 7:55 pm
I been getting these things for decades. Bad enough in mail now they email me. They keep emailing years after stop paying for the site.