Google Kills 200 Ad-Injecting Chrome Extensions, Says a Third Were Malware
Lenovo may have backtracked from using a dangerously unsafe ad injector to make a few extra dollars off of its customers, but they weren’t the only bad actor out there.
Google reported on Tuesday that it was stepping up its efforts to crack down on ad injectors in Chrome. The ad network revealed that it had conducted a study which looked at users who visited Google sites, and examined the users web browsers for malware, ad injectors, and other safety issues.
The researchers worked to identify ad injectors and other potentially unwanted software which both degraded a user’s browsing experience and wasted advertisers money.
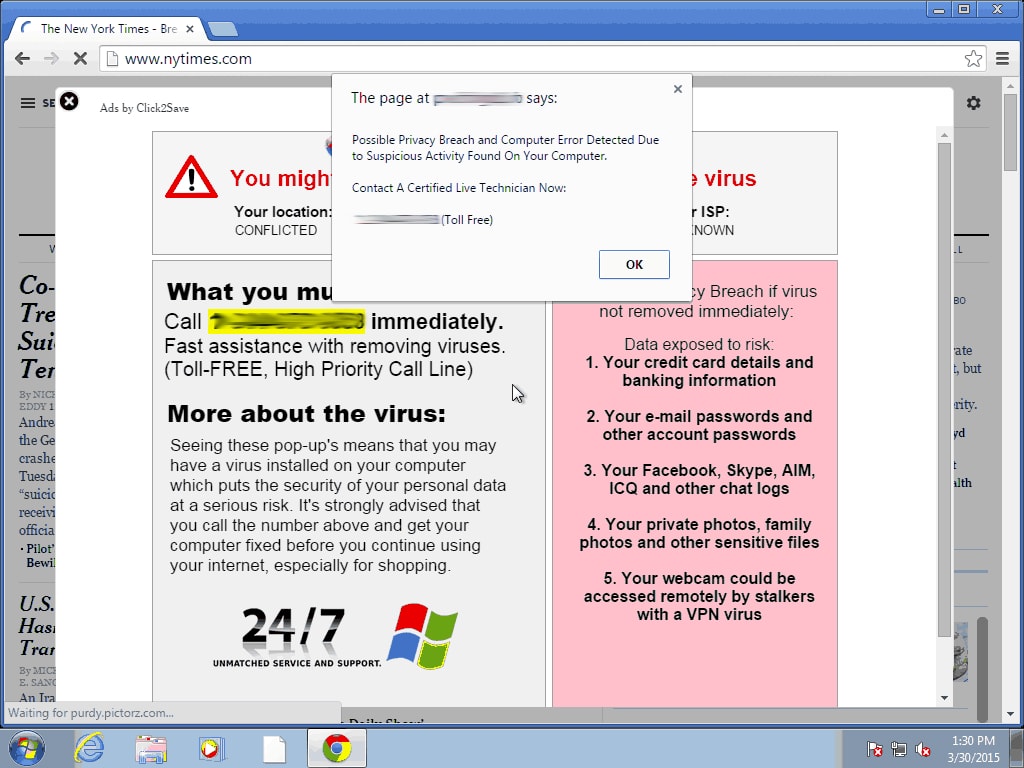
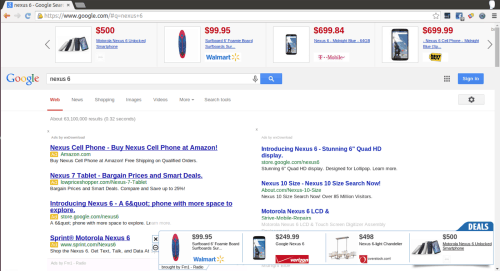
For example, here is a browser with a couple ad injectors taking screen real estate away from the Google-supplied ads in the middle (oh, the horror).
Over 100 million pageviews were logged by Google and its partner, University of California Berkeley. The full details won’t be released until next month, but Google told us yesterday that ad injectors were found on all web browsers (Chrome, Firefox, IE) and OSes (Windows OSX) included in the test.
Five percent of the subjects of the study had at least one ad injector screwing up their browsing experience, and within that group half had at least two injectors installed and nearly one-third have at least four installed.
To make matters worse, Google also identified 192 Chrome extensions, some of which were found in Chrome Web Store, that had deceived users into installing them. Google hasn’t said what those extensions were doing, but it’s safe to assume that injecting adverts was the least of their crimes. A full third of the Chrome extensions injecting ads were classified as outright malware, which suggests that the extensions were likely either being used to attack the user or perhaps as part of a coordinated attack on a website.
Google doesn’t forbid ad injectors, per se, but they do require that an extension’s developer disclose that detail. And to make sure that they do, Google has said that it will be taking the security checks developed in the study, and incorporating them into future scans of all new and updated extensions.
Sadly, that’s only going to catch a tithe of the problem. As we learned in the Lenovo Superfish scandal back in February, users can get ad injectors from seemingly innocuous sources, including a laptop manufacturer. In that situation, Lenovo was caught installing an ad injector which was so poorly designed that it compromised the safety and security of its victim’s computers.
But Google is taking other steps to fight ad injectors and other malware. It recently changed the advertiser rules in AdWords to forbid advertisers from taking a popular app (Firefox, for example) and bundling it with potentially unwanted programs (PUP) like ad injectors.
Have you ever Googled "Firefox download" and seen the first links lead to all sorts of sites other than Mozilla’s official download site? Those ad links are now banned.
Unfortunately, these are just two small parts of the larger problem which is online advertising.
Comments
Are Google's Search Results Promoting Genocide Denial? | Ink, Bits, & Pixels April 29, 2015 um 11:11 am
[…] Google eventually realized those ads were harming users, and changed its advertiser policy to forbid the bundled installers. […]
Security or Domination? Google Blocks All External Chrome Extensions on Windows | Ink, Bits, & Pixels May 13, 2015 um 3:27 pm
[…] months of Google talking up security problems with browser extensions, here is a bit of news which comes as no […]